- SnapLogic - Integration Nation
- Patterns
- Encrypt and decrypt sensitive data in a source
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
Encrypt and decrypt sensitive data in a source
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
10-22-2018 02:10 PM
Created by @pavan
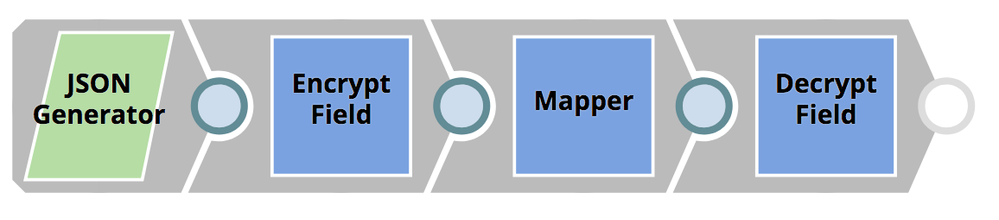
This pipeline pattern will encrypt fields passed as JSON docs using a defined transform type (AES), and decrypts and gives back the original message. This pattern is useful for encrypting sensitive messages (credit card info, SSN, patients name, DOB etc).
Configuration
Within the JSON Generator, replace “Enter certificate here” with your own certificate.
Sources: JSON
Targets: JSON
Snaps used: JSON Generator, Encrypt Field, Mapper, Decrypt Field
Downloads
Encrypt & Decrypt Fields.slp (9.1 KB)
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-15-2019 09:48 AM
Those give away key information on what stratergy is used by an organization for encryption. Also, the attributes I mentioned are key attributes required for encryption.
These are sensitive data.
Pipeline exec vs Iltra ppipeline decision would take this chain in a different direction. Let’s consider the fact that we need to utilize this Ultra pipelines.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-15-2019 10:18 AM
The encryption algorithm in use is not a secret. You can hardcode the algorithm if you want, but it won’t increase security. In some use cases, it can make things less secure since the interface will be stuck with a single algorithm. Then, if that algorithm becomes vulnerable, it will be difficult to change while remaining backwards compatible during the transition period.
No, they are not sensitive. If you don’t want to believe me, please do some of your own research.
Here is a section on IVs in Wikipedia to start:
An initialization vector has different security requirements than a key, so the IV usually does not need to be secret.